YAJ0: Yet Another Java Zero
Through our Malware Protection Cloud (MPC), we detected a brand new Java zero-day vulnerability that was used to attack multiple customers. Specifically, we observed successful exploitation against browsers that have Java v1.6 Update 41 and Java v1.7 Update 15 installed.
Not like other popular Java vulnerabilities in which security manager can be disabled easily, this vulnerability leads to arbitrary memory read and write in JVM process. After triggering the vulnerability, exploit is looking for the memory which holds JVM internal data structure like if security manager is enabled or not, and then overwrites the chunk of memory as zero. Upon successful exploitation, it will download a McRAT executable (MD5: b6c8ede9e2153f2a1e650dfa05b59b99 as svchost.jpg) from same server hosting the JAR file and then execute it.
Figure 1. Example HTTP GET of the McRAT after the browser is successfully exploited, prior to the endpoint becoming fully compromised.
The exploit is not very reliable, as it tries to overwrite a big chunk of memory. As a result, in most cases, upon exploitation, we can still see the payload downloading, but it fails to execute and yields a JVM crash. When the McRAT successfully installs in the compromised endpoint as an EXE (MD5: 4d519bf53a8217adc4c15d15f0815993), it generates the following HTTP command and control traffic:
POST /59788582 HTTP/1.0
Content-Length: 44
Accept: text/html,application/xhtml+xml,application/xml,*/*
User-Agent: Mozilla/5.0 (compatible; MSIE 9.0; Windows NT 6.1; WOW64; Trident/5.0)
Host: 110.XXX.55.187
Pragma: no-cache
4PdWXOD3Vlzg91Zc4PdWXOD3Vlzg91Zc4PdWXMP1RXw.
McRAT persists by writing a copy of itself as a DLL to (C:Documents and SettingsadminAppMgmt.dll) and performing the following registry modifications:
REGISTRYMACHINESYSTEMControlSet001ServicesAppMgmtParameters"ServiceDll" = C:Documents and SettingsadminAppMgmt.dll
REGISTRYMACHINESYSTEMControlSet001ServicesAppMgmtParameters"ServiceDll" = %SystemRoot%System32appmgmts.dll
This post was intended to serve as a warning to the general public. We have notified Oracle and will continue to work with Oracle on this in-the-wild discovery. Since this exploit affects the latest Java 6u41 and Java 7u15 versions, we urge users to disable Java in your browser until a patch has been released; alternatively, set your Java security settings to "High" and do not
execute any unknown Java applets outside of your organization.
We will continue to update this blog as new information about this threat is found. FireEye would like to acknowledge and thank Hermes Bojaxhi and his team at CyberESI for their assistance in confirming this Java zero-day vulnerability.
This blog was written by FireEye researchers Darien Kindlund and Yichong Lin.
Update: Oracle assigned CVE-2013-1493 on this vulnerability
热门曲谱
 渡情笛子曲谱
渡情笛子曲谱 曲谱自学网今天精心准备的曲谱是《渡情笛子曲谱》,下面是详解!
竹笛 我想学 渡情 请问是买A还是B调 的笛子 我还要...
竹笛的调和...
[详情]分类:曲谱大全时间:07:36 c调口琴曲谱
c调口琴曲谱 曲谱自学网今天精心准备的曲谱是《c调口琴曲谱》,下面是详解!
求c调24孔口琴简谱大全
小弟求c调24孔口琴简谱大全,邮箱:zifuchen@st...
[详情]分类:曲谱大全时间:07:36 徳德玛歌曲谱
徳德玛歌曲谱 曲谱自学网今天精心准备的曲谱是《徳德玛歌曲谱》,下面是详解!
德德玛歌曲
1. 草原母亲河
[详情]分类:曲谱大全时间:07:36
2. 蓝蓝的马莲花
3. 阿妈的... 京剧青衣曲谱
京剧青衣曲谱 曲谱自学网今天精心准备的曲谱是《京剧青衣曲谱》,下面是详解!
京剧老旦唱段曲谱 与琴谱有什么区别
两者均属旦行。旦行包括:青...
[详情]分类:曲谱大全时间:07:35 诺言钢琴曲谱
诺言钢琴曲谱 曲谱自学网今天精心准备的曲谱是《诺言钢琴曲谱》,下面是详解!
洛洛历险记的片尾曲诺言的钢琴简谱(最好有前奏)
偶然听见这首歌觉得...
[详情]分类:曲谱大全时间:07:34 流行口琴曲谱
流行口琴曲谱 曲谱自学网今天精心准备的曲谱是《流行口琴曲谱》,下面是详解!
适合初学者的口琴简谱,要流行音乐的
我把爱铺成蓝天 ...
[详情]分类:曲谱大全时间:07:35 又见山里红曲谱
又见山里红曲谱 曲谱自学网今天精心准备的曲谱是《又见山里红曲谱》,下面是详解!
又见山里红简谱
分类:曲谱大全时间:07:31 钢琴流行曲谱
钢琴流行曲谱 曲谱自学网今天精心准备的曲谱是《钢琴流行曲谱》,下面是详解!
有没有流行歌曲的钢琴简谱
樱花草,老人与海,爱转角等。谢谢。本人急...
[详情]分类:曲谱大全时间:07:29 古筝乡韵曲谱
古筝乡韵曲谱 曲谱自学网今天精心准备的曲谱是《古筝乡韵曲谱》,下面是详解!
古筝 乡韵
乡韵多难?既然云裳诉是它改的,乡韵应该也很难吧,特长生...
[详情]分类:曲谱大全时间:07:27 初学古琴曲谱
初学古琴曲谱 曲谱自学网今天精心准备的曲谱是《初学古琴曲谱》,下面是详解!
请问初学者如何识古琴谱,对谱怎么弹?
减字谱:
[详情]分类:曲谱大全时间:07:27
识谱还是比... 一生无悔曲谱
一生无悔曲谱 曲谱自学网今天精心准备的曲谱是《一生无悔曲谱》,下面是详解!
基督教歌曲为福音一生无悔谱
基督教歌曲为福音一生无悔谱...
...[详情]分类:曲谱大全时间:07:26 手机曲谱软件
手机曲谱软件 曲谱自学网今天精心准备的曲谱是《手机曲谱软件》,下面是详解!
在手机上怎么制作谱子
没试过用手机做谱子,效率太低了…
[详情]分类:曲谱大全时间:07:22
建... 渴望主题曲谱
渴望主题曲谱 曲谱自学网今天精心准备的曲谱是《渴望主题曲谱》,下面是详解!
渴望的简谱
《渴望》的简谱是电视剧《渴望》录制的同名主题曲...
[详情]分类:曲谱大全时间:07:22 乐伶曲谱在哪
乐伶曲谱在哪 曲谱自学网今天精心准备的曲谱是《乐伶曲谱在哪》,下面是详解!
天涯明月刀ol乐伶曲谱怎么获得
首先你要学会第一职业 第二行里面...
[详情]分类:曲谱大全时间:07:21 天刀童话曲谱
天刀童话曲谱 曲谱自学网今天精心准备的曲谱是《天刀童话曲谱》,下面是详解!
天涯明月刀ol文士曲谱有哪些
笛曲·水云游 由身份技能点...
[详情]分类:曲谱大全时间:07:20 天刀曲谱弹琴
天刀曲谱弹琴 曲谱自学网今天精心准备的曲谱是《天刀曲谱弹琴》,下面是详解!
天涯明月刀乐伶怎么弹琴给别人加BUF
1:要想加BUF,首先游戏中...
[详情]分类:曲谱大全时间:07:20 天竺少女曲谱
天竺少女曲谱 曲谱自学网今天精心准备的曲谱是《天竺少女曲谱》,下面是详解!
天竺少女的古筝谱
分类:曲谱大全时间:07:18 绿岛小夜曲曲谱
绿岛小夜曲曲谱 曲谱自学网今天精心准备的曲谱是《绿岛小夜曲曲谱》,下面是详解!
绿岛小夜曲原唱晋秦歌词和谱曲
绿岛小夜曲原唱晋秦歌词和谱曲...[详情]
分类:曲谱大全时间:07:17 越剧曲谱下载
越剧曲谱下载 曲谱自学网今天精心准备的曲谱是《越剧曲谱下载》,下面是详解!
求越剧简谱
吴凤花的《狸猫换太子》拷寇部分,三次举起无情棒的曲谱,...
[详情]分类:曲谱大全时间:07:13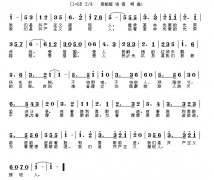 萨克斯曲谱简谱
萨克斯曲谱简谱 曲谱自学网今天精心准备的曲谱是《萨克斯曲谱简谱》,下面是详解!
学萨克斯要学五线谱还是简谱
学萨克斯必须学五线谱。
[详情]分类:曲谱大全时间:07:37
其实...